Cybersecurity in financial services is critical because these institutions are prime targets for cybercriminals. The rise of ransomware, phishing, and nation-state attacks has made financial organizations vulnerable, with breaches often leading to significant financial losses and shaken public trust. Here's what you need to know:
To simplify compliance and improve security, many institutions are turning to automated solutions like Cycore, which streamline processes, reduce manual effort, and ensure continuous monitoring. The stakes are high - cyberattacks are on the rise, and a strong cybersecurity program is essential to protect both organizations and their customers.
Cybersecurity Regulations Financial Services Must Follow
Financial institutions must navigate a complex web of regulations aimed at safeguarding customer data and ensuring the integrity of their systems. These rules are essential for setting security benchmarks and holding organizations accountable for protecting sensitive information.
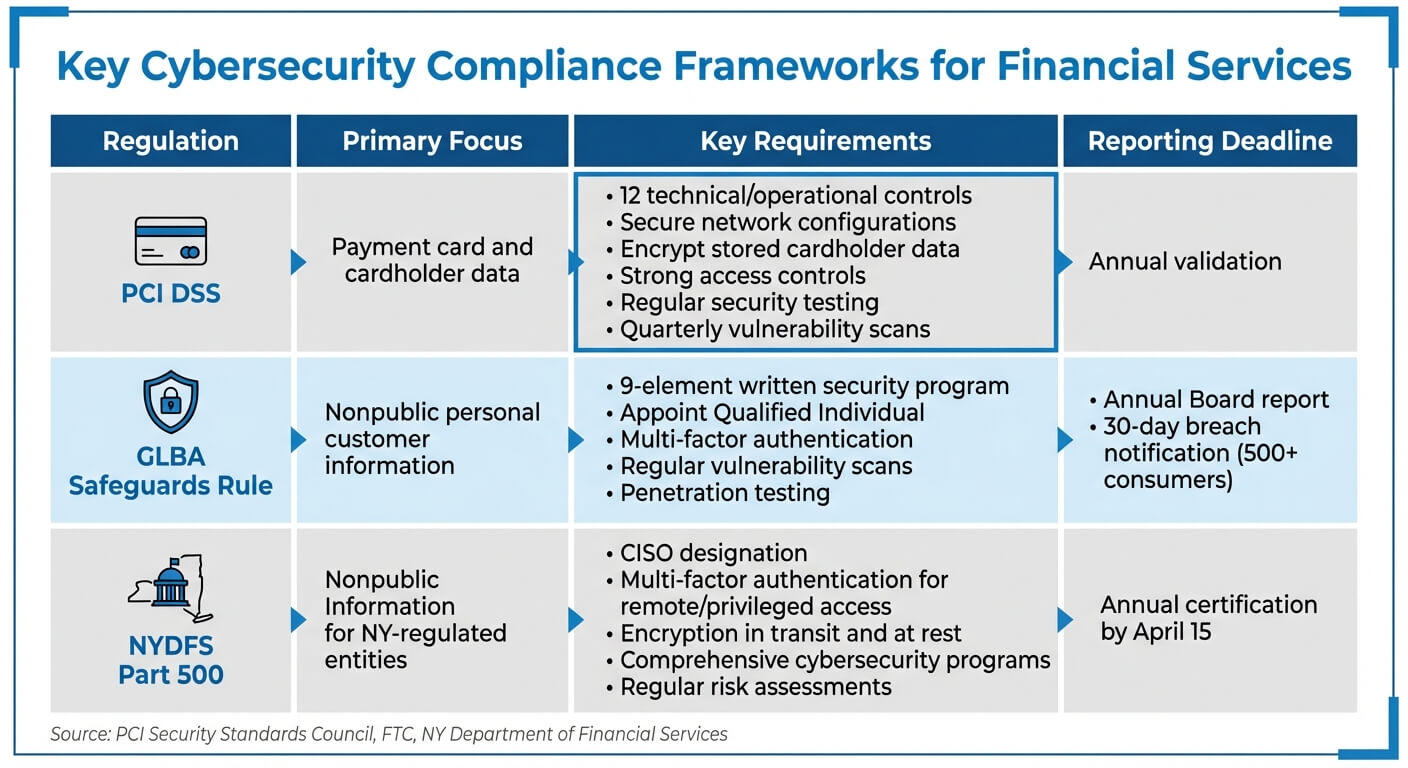
PCI DSS oversees payment card security for entities handling cardholder data, while GLBA (Gramm-Leach-Bliley Act) mandates that non-banking financial institutions implement written security programs to protect personal information. For entities in New York, NYDFS Part 500 adds another layer of oversight, requiring measures like multi-factor authentication and appointing Chief Information Security Officers.
Compliance with these frameworks isn't optional - it’s the cornerstone of any financial institution's cybersecurity strategy. Since these regulations cover various aspects of data protection, most institutions must meet multiple standards at the same time to maintain security and public trust.
PCI DSS: Securing Payment Card Data
The Payment Card Industry Data Security Standard (PCI DSS) outlines 12 technical and operational requirements to safeguard cardholder data. These rules apply to all entities involved in payment card processing, including merchants, processors, and service providers.
PCI DSS provides a baseline of technical and operational requirements designed to protect payment account data.
The focus is on the Cardholder Data Environment (CDE), which includes systems, networks, and processes handling cardholder or sensitive authentication data. Key measures include:
One critical point: never use vendor-supplied default passwords or security settings, as they can be an easy target for attackers. Physical security also plays a role - PCI DSS requires maintaining access logs for at least 90 days and audit trail records for a year.
Compliance involves annual validation, quarterly vulnerability scans (both internal and external), and yearly penetration tests to identify and address potential weaknesses.
GLBA: Privacy and Data Protection Requirements
The Gramm-Leach-Bliley Act (GLBA) demands that non-banking financial institutions create and maintain a written information security program to safeguard nonpublic personal information like customer names, addresses, and bank account details.
A financial institution's information security program is only as effective as its least vigilant staff member.
Institutions must appoint a Qualified Individual to oversee risk assessments, implement safeguards, and report annually to the Board. Multi-factor authentication (MFA) is another requirement, combining at least two factors such as passwords, security tokens, or biometric data.
In 2023, the FTC updated the Safeguards Rule to include breach notification requirements, effective May 2024. Now, institutions must notify the FTC within 30 days of discovering any breach affecting 500 or more consumers. Regular vulnerability scans and penetration tests remain crucial for identifying and addressing risks.
Additional Compliance Frameworks
In addition to PCI DSS and GLBA, financial institutions must adhere to other regulations that often overlap with these core standards.
NYDFS Cybersecurity Regulation (23 NYCRR Part 500) applies to entities under New York's Banking, Insurance, or Financial Services Law, including foreign bank branches operating in the state. First enacted in 2017 and updated in November 2023, the regulation requires comprehensive cybersecurity programs, regular risk assessments, and written policies.
NYDFS mandates appointing a Chief Information Security Officer (CISO), enforcing multi-factor authentication for remote and privileged access, and encrypting nonpublic information in transit and at rest.
Recent enforcement actions highlight the importance of compliance. For example, PayPal, Inc. entered a Consent Order with NYDFS in January 2025, Coinbase, Inc. settled with the agency in January 2023, and First American Title Insurance Company resolved a cybersecurity case in November 2023.
The table below summarizes key elements of these frameworks:
Regulation
Primary Focus
Key Requirement
Reporting Deadline
Payment card and cardholder data
12 technical/operational controls
Annual validation
Nonpublic personal customer information
9-element written security program
Annual Board report; 30-day breach notification
Nonpublic Information for NY-regulated entities
CISO designation, MFA, encryption
Annual certification by April 15
The Federal Financial Institutions Examination Council (FFIEC) adds another layer of guidance with interagency standards and handbooks. These resources focus on areas like authentication, access control, and cloud computing security. While not regulatory mandates, they provide practical advice for implementing security measures.
When conducting risk assessments, institutions should use recognized methodologies such as the NIST Cybersecurity Framework or the CRI Profile. The New York Department of Financial Services emphasizes the importance of these assessments:
The Risk Assessment... is the foundation of the comprehensive cybersecurity program required by DFS's Cybersecurity Regulation.
Risk assessments should be updated at least annually or whenever significant changes occur, such as mergers or new third-party vendors. For vendors, don’t just rely on certifications - perform thorough due diligence to understand the risks they pose.
These regulations provide a roadmap for implementing strong cybersecurity measures and managing third-party risks effectively.
sbb-itb-ec1727d
How to Strengthen Your Cybersecurity Program
Understanding the rules and regulations around cybersecurity is one thing. Building a program that actually protects your organization is another. The good news? Many compliance frameworks share common ground. By implementing strong technical controls, managing vendor risks, and training employees effectively, you can meet multiple standards while reducing actual risks.
Setting Up Technical Security Controls
Technical controls are the foundation of your defense strategy. Start with multi-factor authentication (MFA), which requires users to verify their identity using at least two factors before accessing customer information.
Encryption is non-negotiable. Secure customer data both in transit and at rest. If encryption isn’t possible for certain systems, a Qualified Individual must approve alternative measures that offer equivalent protection.
Implement least privilege access by ensuring users only have access to the systems they need for their roles. Regularly review and update permissions. For highly sensitive systems, use dual control procedures to ensure no single individual has complete control.
Vulnerability management is another key area. The FTC Safeguards Rule requires annual penetration testing and bi-annual vulnerability scans. Continuous monitoring can reduce the need for frequent scans, but most organizations still need the twice-a-year baseline.
Cybersecurity is the process of protecting information by preventing, detecting, and responding to attacks. -
Don’t forget monitoring and logging. Your systems should track user activity, flag unauthorized access attempts, and maintain detailed audit trails. Network segmentation and system hardening further protect against attackers who breach one part of your infrastructure.
When it comes to secure disposal, paper records should be shredded, and electronic media requires advanced data-clearing techniques. Generally, customer information should be disposed of within two years of its last use unless there’s a valid business or legal reason to keep it.
Control Category
Key Technical Measures
MFA, Least Privilege, Dual Control, Password Hashing
Encryption, Secure Disposal, Data Inventory
Firewalls, IDS/IPS, Network Segmentation, Hardening
Penetration Tests, Vulnerability Scans, Audit Trails
Incident Response, Business Continuity, Disaster Recovery
Periodic data inventories are essential to identify all information assets before applying these controls. Also, integrate security assessments into your change management process to ensure new systems don’t compromise existing safeguards.
Controlling Third-Party Vendor Risks
Once you’ve established strong internal controls, extend your focus to third-party vendors. These partners often pose significant risks, yet you remain accountable for their actions under regulatory standards.
A banking organization can be exposed to adverse impacts, including substantial financial loss and operational disruption, if it fails to appropriately manage the risks associated with third-party relationships. - Interagency Guidance on Third-Party Relationships
Vendor risk management should follow a life cycle: Planning, Due Diligence and Selection, Contract Negotiation, Ongoing Monitoring, and Termination. During due diligence, examine a vendor’s financial stability, operational capabilities, and security program. Don’t just take certifications at face value - review independent audits like SOC reports.
Pay close attention to contract terms. Include clauses for audit rights, data destruction upon termination, and mandatory breach notifications. Contracts should also require vendors to implement measures that protect customer information.
The threat landscape is evolving quickly. Recent vulnerabilities, such as those in CitrixBleed and MOVEit, have allowed attackers to target multiple institutions through shared technology. Address fourth-party providers - subcontractors used by your vendors - explicitly in your risk management program.
Pair network segmentation with MFA to limit the fallout if a third-party system is compromised. Include key vendors in your Incident Response Plan testing to ensure they’re prepared for emergencies. Ongoing monitoring is critical - validate that vendors are meeting their contractual obligations and maintaining strong security controls.
Life Cycle Stage
Key Activities
Assess risks, align with goals, plan exit strategies
Evaluate financial health, security, and compliance
Define performance metrics, audit rights, and obligations
Review audits, performance, and any leadership changes
Manage data return/destruction and provider transitions
Training Employees on Security Threats
Even with the best tools and processes, employees remain a critical vulnerability. Human error accounts for 95% of breaches, and about 90% of attacks begin with phishing or social engineering.
Training should be customized and role-specific. For example, system administrators, developers, and executives face different risks and need tailored guidance. Core topics should include phishing awareness, password hygiene, system patching, and incident reporting protocols.
Phishing simulations are highly effective. These realistic exercises teach employees to recognize and report suspicious emails. Track metrics like click rates and post-training assessments to pinpoint areas for improvement.
Your people are not only your greatest asset. They can also pose as your biggest risk. -
Move beyond annual refreshers. Offer monthly or quarterly training sessions to keep employees updated on emerging threats, like quishing (QR code phishing), which has recently targeted financial institutions.
Foster a reporting culture where employees feel encouraged to report suspicious activity without fear of punishment. Tabletop exercises can also help staff practice their roles in incident response plans, ensuring clarity and coordination during a real breach.
The stakes are high. After a breach, 31% of customers sever ties with the affected company, and 65% lose trust in the organization. A strong training program isn’t just about compliance - it’s about protecting your reputation and customer relationships.
How Cycore Handles Compliance and Security for Financial Services
Cycore offers integrated, automated solutions to tackle the ongoing compliance and security hurdles faced by financial institutions. With overlapping frameworks, manual evidence collection, and relentless regulatory oversight, building a robust cybersecurity program is no small feat. Cycore steps in as a dedicated partner, functioning as an embedded security and compliance team that puts essential controls into place.
What Cycore Does for Financial Institutions
Cycore manages the entire compliance process, starting with gap assessments based on frameworks like NIST CSF. From there, they create a tailored written information security program (WISP) to meet GLBA requirements.
Next, Cycore focuses on technical control implementation. This involves putting safeguards in place to protect sensitive customer and cardholder data, all aligned with industry best practices. But these aren't cookie-cutter solutions - Cycore configures your systems, sets up logging, and gathers the evidence auditors require.
For third-party risk management, Cycore leverages the CRI Cyber Profile framework, which aligns with global regulatory expectations. This framework includes over 318 control objectives and 200+ diagnostic statements. Cycore’s system integrates with more than 400 tools to collect evidence and performs over 1,200 tests every hour. It also addresses risks posed by fourth-party providers - those subcontractors your vendors rely on - ensuring they’re included in your risk management strategy.
Beyond these automated controls, Cycore enhances security through a thoughtful mix of AI technology and expert human oversight.
Combining AI Automation with Security Experts
Cycore combines the efficiency of AI with the insight of human experts. AI agents handle time-consuming tasks like evidence collection, gap analysis across frameworks, and remediation support. This eliminates the need for manual tasks like taking screenshots, filling out spreadsheets, or chasing down documentation.
Meanwhile, security experts focus on strategy, risk decisions, and ensuring accuracy. They oversee the AI’s execution, ensuring it aligns with your business goals and compliance needs. This hybrid approach delivers faster results, minimizes errors, and cuts costs compared to traditional manual methods.
"The CRI Profile is incredibly valuable today because of its scalable, risk-based framework that can evolve with technological shifts while maintaining regulatory alignment across a wide range of jurisdictions." - Ethan Heller, GRC Subject Matter Expert
With this model, Cycore replaces traditional point-in-time audits with continuous monitoring. Real-time dashboards and a Public Trust Center allow you to demonstrate compliance to regulators and customers at any time. In contrast, manual in-house processes often rely on periodic reviews, leaving potential security gaps between audits.
Why Financial Services Choose Cycore
Financial institutions are drawn to Cycore because it simplifies compliance by consolidating overlapping requirements from multiple standards - like CRI Cyber Profile, SOC 2, ISO 27001, and DORA - into one unified framework. This eliminates the redundancy that often plagues manual compliance programs.
Another key advantage is the reduced workload. Instead of manually validating over 300 controls, Cycore’s AI automates these tasks, freeing up your team to focus on strategic priorities. Implementation costs for frameworks like the CRI Profile can range from $5,000 to $50,000, depending on your system’s maturity. Cycore’s fixed monthly fee model makes these costs predictable and easier to manage.
Cycore also ensures quicker compliance timelines. With regulatory standards tightening, their unified framework not only simplifies compliance but also allows your team to concentrate on core business operations. The upcoming 2025 retirement of the FFIEC Cybersecurity Assessment Tool (CAT) has led many financial institutions to adopt the CRI Cyber Profile as the new standard. Cycore’s cross-mapping features enable you to reuse evidence from existing controls, such as SOC 2, to prepare for frameworks like CRI or GLBA. This "map once, comply many" strategy keeps you audit-ready year-round, avoiding the last-minute scramble before deadlines.
Conclusion
Main Points to Remember
In 2024, financial institutions faced 23% of all cyberattacks, with 84% of targeted organizations suffering breaches. The financial services sector saw an average data breach cost of $6.08 million - 22% higher than the global average. Compliance frameworks like PCI DSS, GLBA, NYDFS Part 500, and DORA are now stricter, requiring phishing-resistant MFA, detailed asset inventories, and quicker incident reporting. Third-party vendors remain a major weak point, making it essential to implement strong technical controls, include "right-to-audit" clauses in vendor contracts, and train employees to spot and respond to potential threats.
Cycore offers a way to turn compliance into a seamless, automated process. Instead of relying on manual evidence collection and scrambling for audits, their AI-driven solution simplifies compliance while maintaining expert oversight.
The urgency to act is clear.
What Financial Institutions Should Do Next
To tackle these challenges, start by assessing your current security and compliance posture using frameworks like NIST CSF 2.0 or the CRI Cyber Profile to uncover vulnerabilities. Strengthen your defenses with phishing-resistant MFA, and treat risk assessments as ongoing processes, updating them whenever your technology or vendor relationships change. Formalize your incident response plan and conduct tabletop exercises to ensure your team is prepared for real-world scenarios.
If managing compliance manually feels overwhelming, consider partnering with Cycore to automate evidence collection and close compliance gaps. With phishing attacks surging nearly 1,200% since the rise of AI, the risks of inaction are too high. Cycore’s fixed monthly fee model provides predictable costs, faster compliance, and hands-on support - helping you stay ahead of both attackers and regulators.
FAQs
Which cybersecurity rules apply to my financial institution?
Financial institutions are required to adhere to regulations such as Part 500 from the New York State Department of Financial Services. This regulation covers key areas like cybersecurity programs, policies, risk assessments, and third-party security measures. Beyond that, guidance from entities like the FFIEC, FDIC, and the Federal Reserve emphasizes critical aspects of risk management, incident reporting, and safeguarding essential infrastructure. Together, these frameworks play a central role in ensuring strong cybersecurity practices and maintaining compliance within the financial sector.
What should we do first to reduce breach risk fast?
To cut down breach risks fast, prioritize strict identity and access management (IAM) policies. Start with key measures like:
These steps go a long way in safeguarding critical information and reducing potential vulnerabilities.
How can we monitor third-party vendor security continuously?
Continuous monitoring of third-party vendor security means keeping a close eye on their practices through regular assessments, real-time cybersecurity ratings, and frequent reviews of compliance and risk reports. To stay on top of this, leverage tools and frameworks specifically built for continuous oversight. These help ensure vendors consistently align with security and regulatory standards.
Related Blog Posts
- Solving Common vCISO Implementation Challenges
- 2025 Security Compliance Requirements for Fintech
- Cybersecurity Regulations Coming in 2026 - Early Look
- The Worst Healthcare Data Breaches in 2025: A Recap
{"@context":"https://schema.org","@type":"FAQPage","mainEntity":[{"@type":"Question","name":"Which cybersecurity rules apply to my financial institution?","acceptedAnswer":{"@type":"Answer","text":"<p>Financial institutions are required to adhere to regulations such as <strong>Part 500</strong> from the New York State Department of Financial Services. This regulation covers key areas like cybersecurity programs, policies, risk assessments, and third-party security measures. Beyond that, guidance from entities like the <strong>FFIEC</strong>, <strong><a href=\"https://www.fdic.gov/\" target=\"_blank\" rel=\"nofollow noopener noreferrer\">FDIC</a></strong>, and the <strong><a href=\"https://www.federalreserve.gov/\" target=\"_blank\" rel=\"nofollow noopener noreferrer\">Federal Reserve</a></strong> emphasizes critical aspects of risk management, incident reporting, and safeguarding essential infrastructure. Together, these frameworks play a central role in ensuring strong cybersecurity practices and maintaining compliance within the financial sector.</p>"}},{"@type":"Question","name":"What should we do first to reduce breach risk fast?","acceptedAnswer":{"@type":"Answer","text":"<p>To cut down breach risks fast, prioritize strict <strong>identity and access management (IAM)</strong> policies. Start with key measures like:</p> <ul> <li><strong>Multi-factor authentication (MFA)</strong>: Adds an extra layer of security by requiring multiple forms of verification.</li> <li><strong>Single sign-on (SSO)</strong>: Simplifies access while maintaining control over who gets in.</li> <li><strong>Biometrics</strong>: Ensures only authorized individuals can access sensitive data through unique physical traits.</li> </ul> <p>These steps go a long way in safeguarding critical information and reducing potential vulnerabilities.</p>"}},{"@type":"Question","name":"How can we monitor third-party vendor security continuously?","acceptedAnswer":{"@type":"Answer","text":"<p>Continuous monitoring of third-party vendor security means keeping a close eye on their practices through <strong>regular assessments</strong>, <strong>real-time cybersecurity ratings</strong>, and <strong>frequent reviews of compliance and risk reports</strong>. To stay on top of this, leverage tools and frameworks specifically built for continuous oversight. These help ensure vendors consistently align with security and regulatory standards.</p>"}}]}