Why Life Sciences Companies Fail Security Audits After Passing FDA Inspections
Passing an FDA inspection doesn’t guarantee success in security audits. While FDA inspections focus on patient safety and device functionality, security audits like SOC 2 and ISO 27001 evaluate broader organizational cybersecurity. This mismatch in priorities often leaves companies unprepared for audit requirements, risking customer trust, financial losses, and compliance delays.
Key Reasons for Audit Failures:
- Narrow FDA Scope: FDA focuses on device-specific safety, while audits assess enterprise-wide systems, including HR, finance, and IT.
- Legacy Systems: Older systems often lack modern security features like encryption and multifactor authentication.
- Third-Party Risks: Poor vendor oversight leads to compliance gaps, especially in breach notification and data protection.
- Weak Access Controls: Outdated policies allow unnecessary access, creating vulnerabilities.
How to Align FDA and Security Audit Standards:

- Map FDA rules to security frameworks (e.g., ISO 13485 to ISO 27001).
- Implement continuous monitoring for real-time compliance tracking.
- Strengthen third-party risk management with clear vendor agreements.
- Invest in automation tools to streamline evidence collection.
- Train employees on cybersecurity best practices and incident reporting.
By addressing these gaps, companies can safeguard operations, meet customer expectations, and avoid costly setbacks.
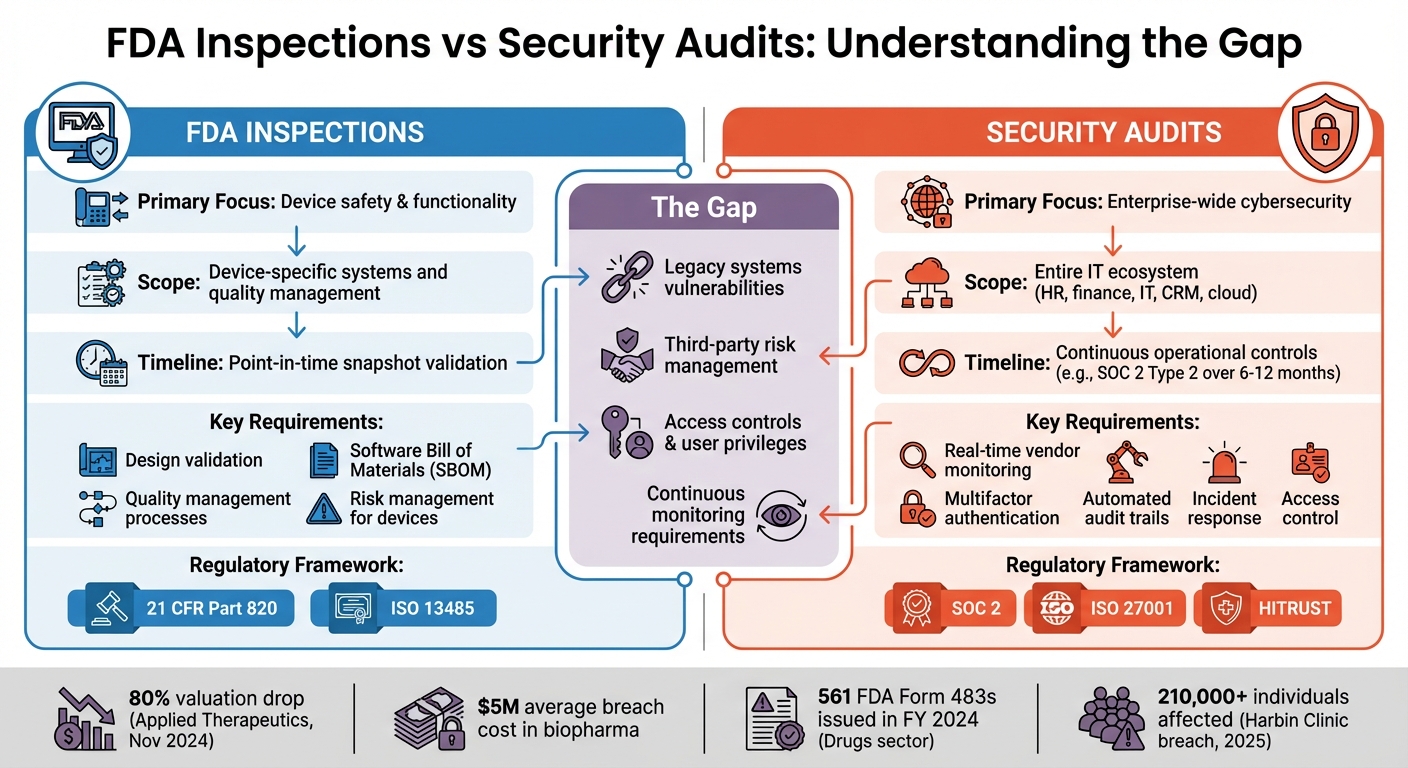
FDA Inspection vs Security Audit Requirements Comparison
Why Life Sciences Companies Fail Security Audits
FDA Inspections Cover Only Part of Security Requirements
FDA inspections focus on ensuring device safety through design and quality management processes, but security audits take a much broader approach. Audits like SOC 2 or ISO 27001 evaluate the organization's entire IT ecosystem, covering everything from HR platforms to financial systems and customer relationship tools. This goes far beyond the scope of FDA inspections, which concentrate primarily on device safety.
FDA inspections typically provide a snapshot in time, validating compliance at a specific moment. In contrast, SOC 2 Type 2 audits assess operational controls over an extended period. For instance, while an FDA inspection might confirm the inclusion of a Software Bill of Materials (SBOM) for third-party components, security audits require ongoing processes to monitor and evaluate the cybersecurity practices of all third-party vendors. This includes entities like cloud service providers, payroll systems, and marketing platforms, which FDA reviews do not typically address.
"Because healthcare organizations primarily focus on meeting HIPAA requirements, they may lack the resources or expertise to implement the wider technical and administrative controls SOC 2 requires." – Vanta
This disconnect highlights why legacy systems often amplify these challenges.
Legacy Systems Create Security Vulnerabilities
Legacy systems, including outdated lab equipment, often lack essential security features like automated audit trails, strong encryption, and multifactor authentication. While these systems may meet FDA standards due to their established clinical utility, they typically fall short of modern security audit requirements, which demand active support and the ability to apply patches.
A stark example of the risks tied to outdated systems occurred in November 2024. Applied Therapeutics saw its valuation plummet by 80% - from $10.21 to $2.03 in just three days - after the FDA rejected its drug application over software-related compliance issues. Additionally, legacy platforms often have weak access controls, enabling unauthorized data changes and failing to provide clear user activity logs.
"Legacy devices will be unable to meet these [new FDA] requirements, but there are no exceptions in the statute, and FDA did not offer enforcement discretion in the guidance." – Ariel Z. Seeley, Of Counsel, Morgan Lewis
Another issue with legacy systems is configuration drift. Over time, systems can deviate from their original approved state - a phenomenon known as "510(k) drift." These unapproved changes can result in non-compliance with the original regulatory submission. Acquisitions can further complicate matters, as companies often inherit outdated records and systems with hidden security vulnerabilities that auditors later flag.
These challenges are only magnified when third-party management falls short.
Gaps in Third-Party Risk Management
Many companies mistakenly assume that outsourcing shifts both regulatory and security responsibilities to their vendors. While the FDA mandates supplier qualifications for GxP compliance, security audits require continuous oversight of a vendor's cybersecurity measures. Agreements like Business Associate Agreements (BAAs) or Quality Agreements may satisfy basic regulatory needs but often lack detailed security protocols. For example, they may not require breach notifications within 24 to 48 hours or secure data disposal practices aligned with NIST guidelines.
A real-world example of third-party risk mismanagement occurred in May 2025. Harbin Clinic had to notify over 210,000 individuals of a PHI breach linked to its vendor, Nationwide Recovery Services (NRS). The breach was discovered in July 2024, but the vendor didn't inform the clinic until February 2025 - a seven-month delay that highlights the lack of proper oversight. Unlike FDA compliance, which relies on periodic supplier audits, security audits demand real-time monitoring and rapid incident response.
"Regarding breaches due to third parties, the fundamental thing that needs to be done is setting up a robust third-party risk management program. There are no shortcuts." – Lee Kim, Senior Principal of Cybersecurity and Privacy, HIMSS
Another overlooked risk lies in manufacturing equipment, which often contains components from undisclosed sub-vendors. Without visibility into these components, companies struggle to inventory their network assets, a common requirement for security audits. For example, in July 2024, a flawed software update from CrowdStrike caused global outages, including in hospitals and government agencies, resulting in $5 billion in losses over just four days.
Poor Access Controls and User Privilege Management
Weak access control policies are another major reason life sciences companies fail security audits. Legacy systems often cannot enforce role-based access or maintain detailed logs of user activity. Manual provisioning processes contribute to "privilege creep", where employees accumulate unnecessary access rights over time, creating vulnerabilities.
Security audits demand stricter measures like multifactor authentication, automated deprovisioning for departing employees, and regular reviews of user privileges. While FDA inspections might check whether a quality control unit approves procedures affecting drug identity and strength, they don't evaluate whether HR systems enforce proper access controls or if former employees still have access to sensitive networks. In FY 2024, the FDA issued 561 Form 483s in the Drugs sector, with many citing data integrity gaps linked to poor access management.
Temporary privileged accounts, often created for vendor deployments, add another layer of risk. These accounts may remain active long after the work is completed, leaving companies exposed to potential breaches. Without automated systems to track and revoke these permissions, demonstrating continuous control effectiveness becomes a significant challenge.
sbb-itb-ec1727d
How to Align FDA Compliance with Security Audit Standards
Map FDA Requirements to Security Frameworks
The FDA's Quality Management System Regulation (QMSR), effective February 2, 2026, now integrates ISO 13485:2016 standards. This alignment makes it easier to connect FDA requirements with security frameworks like ISO 27001 and SOC 2. By using ISO 13485 as a starting point, you can map quality controls to security needs. For instance, Risk Management (Clause 7.1) in ISO 13485 corresponds to the "Identify" function in the NIST Cybersecurity Framework, while Design Validation (Clause 7.3.7) aligns with security-by-design principles in ISO 27001.
The FDA encourages leveraging the NIST Framework for Improving Critical Infrastructure Cybersecurity to create a shared language for regulatory and security audit requirements. This framework’s five functions - Identify, Protect, Detect, Respond, and Recover - serve as a practical guide for documenting controls that meet both FDA and security audit standards.
| FDA Requirement | Security Framework Alignment | Shared Documentation |
|---|---|---|
| SBOM for cyber devices | Third-party risk management (SOC 2, ISO 27001) | Vendor component inventory |
| Risk Management (ISO 13485 Clause 7.1) | NIST CSF "Identify" function | Risk register and treatment plans |
| Design Validation (ISO 13485 Clause 7.3.7) | Security-by-design (ISO 27001) | Threat modeling documentation |
| CAPA (ISO 13485 Clause 8.5) | Incident response (SOC 2) | Corrective action records |
Once these controls are mapped, continuous monitoring becomes essential for maintaining compliance across both FDA and security audit standards.
Set Up Continuous Monitoring and Incident Response
While FDA inspections focus on a specific point in time, security audits like SOC 2 Type 2 require evidence of operational controls over a longer period. To meet FDA recommendations for "Event Detection and Logging", implement automated logging systems that track user activity, access changes, and configuration updates across all environments - not just medical devices.
Incorporate security incidents into the ISO 13485 CAPA process, and establish Coordinated Vulnerability Disclosure (CVD) procedures. This ensures vulnerabilities are patched effectively and documented with root cause analyses, remediation strategies, and preventive measures.
"Cybersecurity is no longer a standalone technical consideration - it is embedded into Risk Management, Design Controls, Validation Activities, and Postmarket Surveillance." – Maven Regulatory Solutions
The FDA also advises tracking metrics like "defect density" (percentage of patched vulnerabilities) and the time taken to apply patches. These metrics not only demonstrate continuous improvement but also meet security audit requirements for incident response.
Create a Formal Third-Party Risk Management Program
Even when activities are outsourced, FDA-regulated manufacturers remain accountable for ensuring compliance. A strong third-party risk management program must address 21 CFR Part 820 (Purchasing Controls) for medical devices while also meeting vendor security requirements under SOC 2 and ISO 27001.
Start by conducting multi-dimensional risk assessments that evaluate suppliers based on factors like financial stability, geopolitical risks, and the criticality of their components. For vendors handling Protected Health Information (PHI), establish Business Associate Agreements (BAAs) that clearly outline security responsibilities, breach notification timelines (no later than 60 days after discovery), and secure data disposal practices.
"Cybersecurity is another major (and quickly growing) area of concern, especially if a supplier handles sensitive data or is integrated into digital aspects of the manufacturing process." – David Festa, Director of Corporate Quality, Thermo Fisher Scientific
Tailor your audits based on supplier risk levels. For high-risk vendors or those supplying critical components, conduct more frequent and thorough reviews. However, even the best vendor oversight won't be effective without a well-prepared and knowledgeable workforce.
Train Employees on Security Best Practices
Continuous security awareness training is essential. Cover topics like password security, recognizing phishing attempts, proper data handling, and how to report incidents. Keep records of training sessions, including attendance, materials, and test results, as these will demonstrate compliance during audits.
Run quarterly phishing simulations, tracking metrics like click rates, reporting rates, and the time it takes to report suspicious emails. Employees who fail these tests should complete remedial training, with all activities documented to show ongoing improvement - an important aspect of SOC 2 and ISO 27001 compliance.
Provide role-specific training as well. Employees with PHI access need HIPAA-specific training, while developers should be trained in secure coding practices. Keep these records for at least six years to meet HIPAA requirements. Conduct regular tabletop exercises for incident response plans to ensure teams are ready for security events. These exercises also provide valuable evidence of operational readiness for auditors.
Tools and Methods for Maintaining Compliance
Use Compliance Automation to Reduce Manual Work
Relying on manual processes for compliance can eat up valuable time and leave gaps that auditors are quick to notice. Automation platforms provide a solution by continuously gathering evidence from your existing systems - like HRIS, SSO providers, cloud infrastructure, and DevOps tools. This eliminates the need for tedious screenshots and manual log exports. These platforms perform hundreds, sometimes thousands, of automated tests every hour to ensure controls remain effective, immediately alerting you if something falls out of compliance.
The time savings are impressive. Automation can slash framework-related audit work by as much as 82%. When adding a new framework, pre-mapped controls can cut up to 80% of the effort. For life sciences businesses managing FDA requirements alongside frameworks like SOC 2, ISO 27001, or HITRUST, automation allows the reuse of evidence across multiple audits. For instance, incident response documentation prepared for SOC 2 can also fulfill ISO 13485 CAPA processes and meet ISO 27001 standards at the same time.
"The promise of automation has long been discussed in the compliance world, but never truly realized. Drata has turned that into reality." – Jonathan Jaffe, CISO, Lemonade
Automation tools also simplify one of the most common audit stumbling blocks: access reviews. Built-in workflows can automatically identify risky accounts, such as those tied to former employees, and trigger immediate action. For FDA-specific needs like 21 CFR Part 11, many platforms let you create custom frameworks and map unique controls to automated tests, ensuring no requirements slip through the cracks.
By combining automation with comprehensive frameworks, organizations can build scalable and efficient security programs.
Adopt GRC Frameworks for Scalable Security Programs
Frameworks like SOC 2, ISO 27001, and HITRUST offer a unified approach to bridging FDA compliance with broader security goals. These frameworks act as a common language, aligning FDA requirements with general cybersecurity standards. Mapping controls across frameworks allows you to create documentation that satisfies multiple audits at once.
Start by choosing frameworks that align with your business needs. For companies targeting enterprise customers, SOC 2 is a common starting point. If you handle PHI, HIPAA compliance is essential, and adding HITRUST can provide an extra layer of assurance. HITRUST’s e1 (Essential 1) assessment offers a streamlined entry point, while the more advanced r2 (Risk-based 2) level incorporates over 2,000 controls.
Rather than treating frameworks as mere checklists, use them as strategic guides. Set Service Level Objectives (SLOs) for audit readiness, such as ensuring 95% of evidence is accessible within 24 hours or updating policies 30 days before an audit. This shifts compliance from being a reactive, last-minute scramble to an ongoing, manageable process.
Combining automation and frameworks is only part of the equation - keeping audit-ready documentation throughout the year is equally important.
Maintain Audit-Ready Documentation Year-Round
Scrambling to gather evidence at the last minute not only wastes time but also increases the chance of missing critical details. Instead, set up a centralized evidence repository. This could be a GRC platform, SharePoint, or another compliance tool that serves as your single source of truth for policies, access logs, training records, and incident reports. Ensure version control is in place so auditors can see how policies have evolved and when changes were implemented.
Keep your Software Bill of Materials (SBOM) up to date as a living document. Automated tools can monitor third-party components for vulnerabilities, creating an immutable audit trail that meets both FDA cybersecurity requirements and broader security framework standards. Similarly, tools like Terraform or Ansible can manage configuration changes automatically, tracking and documenting updates as they happen.
"The goal is not to focus on audits as discrete events, but to embed audit preparation into your ongoing operational practices - making compliance a continuous process rather than a periodic crisis." – CybersecurityOS
Conclusion: Meeting Security Standards Beyond FDA Compliance
Clearing an FDA inspection is a big step, but it doesn’t mean your enterprise meets all the broader security audit standards out there. The FDA primarily focuses on product safety and data integrity, now formalized through the Quality Management System Regulation (QMSR), which went into effect on February 2, 2026. However, frameworks like SOC 2, ISO 27001, and HITRUST take a much wider view, assessing everything from IT infrastructure and HR practices to physical security and third-party risks. These frameworks are now critical benchmarks for securing partnerships, gaining investor confidence, and handling enterprise-level engagements.
While FDA compliance ensures product safety, broader security audits are about protecting your entire operation - and they can have a direct financial impact. For example, in the biopharma industry, the average cost of a data breach is around $5 million. Between 2018 and 2020, top firms saw breach reports nearly double, from 1,930 to 3,619. And the risks go beyond financial losses. Failing to maintain robust security measures can lead to serious legal consequences. In June 2025, the DOJ settled with Illumina Inc. after whistleblower claims that the company failed to address cybersecurity vulnerabilities in its genomic sequencing products, resulting in misrepresentations in federal grant applications.
"Cybersecurity is no longer a standalone technical consideration - it is embedded into Risk Management, Design Controls, Validation Activities, and Postmarket Surveillance." – Maven Regulatory Solutions
Instead of treating security as a one-time compliance task, think of it as a continuous process integrated into your entire product lifecycle. Start by mapping FDA requirements to broader frameworks like SOC 2, ISO 27001, or HITRUST. Use automation tools to maintain audit-ready documentation, and make sure your security program includes third-party vendors and legacy systems. Taking these steps doesn’t just help you meet compliance - it strengthens your operations, safeguards clinical trial data, and builds the trust you need for sustained growth.
FAQs
What does a SOC 2 or ISO 27001 audit check that an FDA inspection doesn’t?
SOC 2 and ISO 27001 audits take a deep dive into an organization’s security controls and how it manages risks. They focus on critical areas like data protection, access control, and incident response plans. On the other hand, FDA inspections are geared towards ensuring compliance with regulations that prioritize patient safety, product quality, and data integrity.
One key difference? SOC 2 and ISO 27001 audits also emphasize the importance of managing third-party risks and maintaining strong governance practices - something that FDA inspections generally don't cover.
What’s the fastest way to prepare for a SOC 2 Type 2 audit after passing an FDA inspection?
Automation tools paired with ongoing oversight processes can significantly speed up the SOC 2 audit process. Automated compliance solutions are particularly effective in identifying and addressing weak spots, such as issues with access control or vendor risk management, which helps lower the chances of audit failures. By incorporating features like vulnerability management, continuous monitoring, and automated reporting, these tools simplify your security program. This streamlined approach not only aligns your efforts with SOC 2 requirements but also makes the entire audit process quicker and more efficient.
How can we prove our vendors meet security requirements (like breach notice and data disposal)?
To ensure vendors align with your security standards - such as breach notification protocols and data disposal practices - it's essential to use third-party risk management frameworks. Start by conducting security questionnaires, like SIG Lite or CAIQ, to gather detailed insights into their practices. Additionally, review compliance reports such as SOC 2 Type II audits to verify their adherence to industry standards.
Keep a detailed record of all assessments and audits. This documentation not only helps with accountability but also serves as a reference for future evaluations. Implement continuous monitoring to track vendors' compliance over time. Regularly requesting updated attestations from vendors further reinforces transparency and keeps them accountable for maintaining security standards.
Related Blog Posts
- The Top 4 Healthcare Cybersecurity Myths Debunked
- The Worst Healthcare Data Breaches in 2025: A Recap
- From Seed to Series B: The Compliance Roadmap Every Fintech Founder Needs (But No One Explains)
- Life Sciences Compliance 101: Why GxP and Cybersecurity Are Two Different Problems - and Why You Need to Solve Both



.avif)